- cross-posted to:
- security
googleprojectzero.blogspot.com
- cross-posted to:
- security
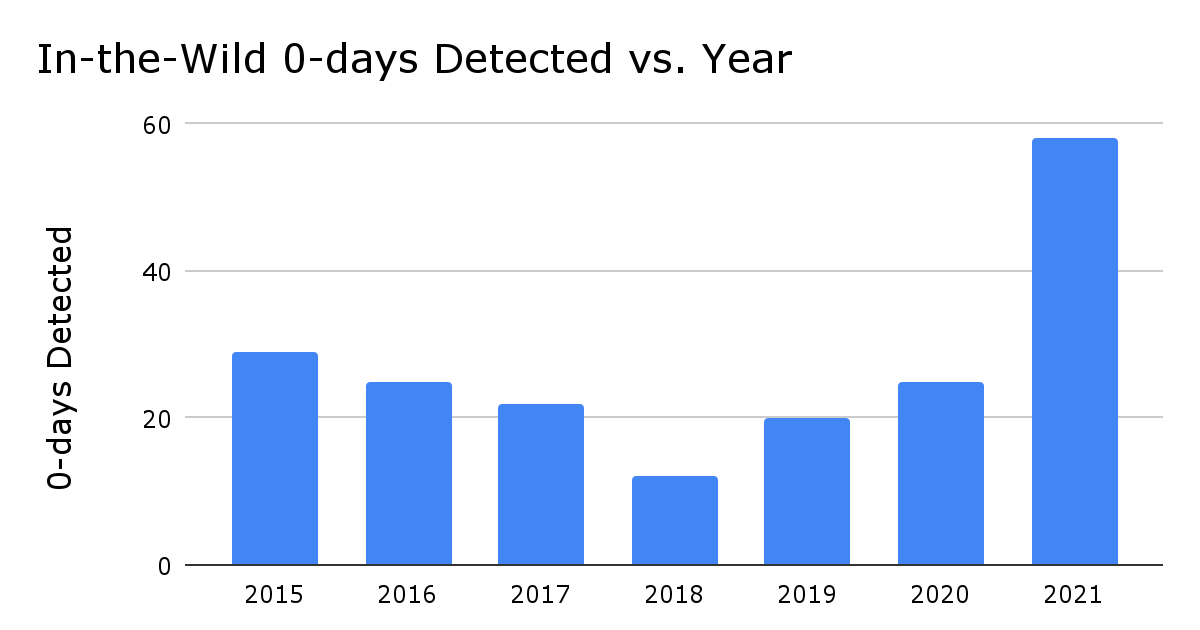
Out of the 58 in-the-wild 0-days for the year, 39, or 67% were memory corruption vulnerabilities. Memory corruption vulnerabilities have been the standard for attacking software for the last few decades and it’s still how attackers are having success. Out of these memory corruption vulnerabilities, the majority also stuck with very popular and well-known bug classes:
- 17 use-after-free
- 6 out-of-bounds read & write
- 4 buffer overflow
- 4 integer overflow
Attackers are having success using vulnerabilities similar to what we’ve seen previously and in components that have previously been discussed as attack surfaces.The goal is to force attackers to start from scratch each time we detect one of their exploits: they’re forced to discover a whole new vulnerability, they have to invest the time in learning and analyzing a new attack surface, they must develop a brand new exploitation method.
This is because developers are fixing single instances of bugs and not the whole classes of them. To address memory corruption bugs as a whole class you need to dramatically change your development practice or even the programing language to a memory safe one. Without doing so it will continue to be a whac-a-mole exercise forever.