

There are Google Analytics trackers on The Intercept website, so here is an excerpt:
Source: https: / / theintercept(dot)com/surveillance-catalogue/stingray-iii/
“Ensnares bystanders, drains batteries, blocks calls”
Review by Nathan Wessler
Staff Attorney with the American Civil Liberties Union’s Speech, Privacy, and Technology Project
This dragnet surveillance workhorse has been deployed for years by numerous local law enforcement agencies across the United States. Don’t worry about the six-figure price tag: A federal grant will cover that. Upside: fierce name. Downsides: ensnares bystanders’ phones within up to 200 meters, drains phones’ batteries by forcing them to broadcast at full power for greater surveillance potential, and can block calls placed by nearby phones. But don’t worry too much: Ready-made non-disclosure agreements from the FBI and Harris Corp. will provide a pretext for concealing these features from the public. If you like the Stingray, you’ll love Harris Corp.’s next-generation Hailstorm, a must-have for cracking the 4G LTE network.
Stingray I/II
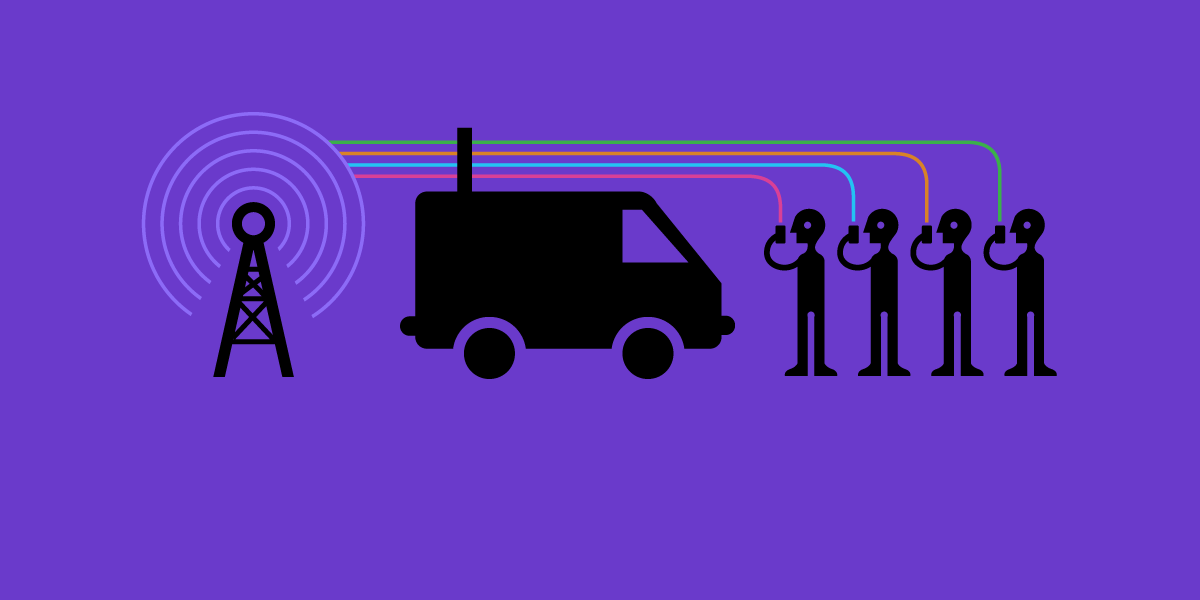
Ground Based Geo-Location (Vehicular)
Capabilities
- Ground GSM/CDMA stimulation device
- Replicates BTS to STIM handset into RF SDCCH allowing for DF
- Passive and active modes of operation
- Optional 5 Watt Amp available
Limitations and Planning Factors
- Approx ground distance 200 Meters
- Target Handset must be on & not engaged in a call
- Cannot DF with Gjallar or Datong system
- Locking handset into SDCCH drains battery and raises signal strength
- Use of system requires deconfliction w/ other geo elements in AO
- Network can identify rogue BTS
- Improper use can impact network
Vendor
Harris Corporation Melbourne, Florida-based Harris Corp. makes the most well-known cell-site simulator technology, the Stingray, used in cellphone surveillance by military intelligence and law enforcement. The company’s May 2015 acquisition of Virginia-based Exelis moved it toward domestic government business, according to industry experts. — Margot Williams, The Intercept
Protocols
900Mhz, 1800Mhz, 850Mhz and 1900Mhz and CDMA (multi-protocol and requires antenna)
Approval
Title 10
Cost: $134,952.00 USD

Maybe(to add): https://searx.neocities.org
Policies:
I found this random Searx/SearXNG search engine redirector at https://searx.space under the About tab.
To use it, I save the search redirector as a bookmark at https://searx.neocities.org/#q=%s&category_general=on
I also turn on javascript on at searx.neocities.org because otherwise I have to type in my search query manually into a specific search instance.
However if your threat model requires it, you can also go to the no-javascript version of searx.neocities.org. You will not be automatically redirected to a random Searx instance when using no-JS version.
I type in a keyword in the url bar and then the service redirects me to a random Searx/SearXNG instance. For load balancing purposes, it seems great since no single server will be stressed significantly. The searches are spread across multiple instances.
Sometimes the redirected Searx/SearXNG instances output bad results(e.g. errors). In that case, just use the Searx redirector again to have new random Searx/SearXNG instance.