This is a very entertaining and educational article, giving insights into the methods used by thiefs to try and get access to your phone data.
I don’t like Apple but it’s great that their security is so good when it comes to this.
the methods used by thiefs to try and get access to your phone data.
It is not about accessing the data but to disassociate the current user from the phone so that the thief can reset the phone or/and it’s components for new users.
Man, the last threat the author received was absolutely BEGGING for the navy seal copypasta lololol
But give them one of the more obscure versions so they don’t immediately realize what it is.
What’s this you’ve said to me, my good friend? Ill have you know I graduated top of my class in conflict resolution, and Ive been involved in numerous friendly discussions, and I have over 300 confirmed friends. I am trained in polite discussions and I’m the top mediator in the entire neighborhood. You are worth more to me than just another target. I hope we will come to have a friendship never before seen on this Earth. Don’t you think you might be hurting someone’s feelings saying that over the internet? Think about it, my friend. As we speak I am contacting my good friends across the USA and your P.O. box is being traced right now so you better prepare for the greeting cards, friend. The greeting cards that help you with your hate. You should look forward to it, friend. I can be anywhere, anytime for you, and I can calm you in over seven hundred ways, and that’s just with my chess set. Not only am I extensively trained in conflict resolution, but I have access to the entire group of my friends and I will use them to their full extent to start our new friendship. If only you could have known what kindness and love your little comment was about to bring you, maybe you would have reached out sooner. But you couldn’t, you didn’t, and now we get to start a new friendship, you unique person. I will give you gifts and you might have a hard time keeping up. You’re finally living, friend.
Hadn’t seen that one before. That’s a good one, lol
Honestly I’m scared of when these people figure out they can use llms to make their texts look like less obvious scams
Often scammers don’t want to make it less obvious. If it’s obvious and the mark falls for it, it’s a good indicator they’re on the hook and will fall for more. It’s to filter out the less gullible so the scammer doesn’t waste their time. Probably not the case with this situation specifically, but it holds true in general with scams.
True. But also true is that a majority of scammers are simply not smart and/or English is not their native language. A phishing email/text that might look good to them, can look really bad to others.
But still, people still fall for the obvious phishing attacks. AI is going to make the phishing appear more legit.
Probably not the case with this situation specifically
Yeah :( High-value item already in hand, never a need to guide somebody which store to buy the giftcard at or what to say to the bank teller…
On a similar note, a reason why you shouldn’t respond to spam/scam texts because it basically verifies you as an active phone number. Why waste man/bot power texting numbers that may or may not exist when a majority of your texts will at least be seen by a human which will probably boost their chance
It’s why I tell my friends not to respond even tho some of their responses are really funny
Some smarter ones I see usually range between 2-7 lines of text usually written as a time sensitive question that will affect the totally real persons social or work like
One of my favorite ones was about 5 lines of text that was posed as a date
It was like “Hey Kayla it’s Mike, some short sob story about dating life, hope our first date goes well, then nonsense about dating with an address thrown in
However after the 5 lines it was in Arabic or some similar flowy characters and when I translated it continued “mikes” story about where he was from and how oh so sad his life was
Tldr totally fishing for a pity “sorry wrong number” to see if my phone number would be seen by human
I’m confused, in the article he said it was a brick to whoever has his stolen phone. How did they get his phone number to send him text messages? Did they crack the passcode and needed the iCloud password?
I think when you remotely wipe the phone you can make it show a message with your phone number, in case you’re actually a honest person that found the phone instead of a thief.
In the response posts to the article someone said they got the icloud address via reset request which you can use in iMessage.
Not an i phone person so i can’t verify but thought id pass that along.
That’s interesting, never thought of that as an attack vector.
The phone itself (by IMEI) is a brick. The sim and same phone number were assigned to a new phone and they texted that number
Issue here is the iPhone 14 USA models are all e-Sim. They don’t have sim cards to remove. The article says it was a iPhone 14 Pro.
Typically if you report the phone stolen to your provider they blacklist the IMEI which gets shared with other providers so the phone can no longer be used. I was unclear on this part but a new e-sim can be provided for the new phone, and the old sim banned or the old one transferred. Regardless, the old phone will still show the IMEI/sim/phone number, which is how they got that to text them
So they took the SIM card out and got the phone number from that? I guess I didn’t realize you could do that.
Yes, it’s the SIM card that carries your number and may also carry data on your contacts if you save it there.
They almost definitely got this info by simply having the IMEI, which is printed on the back and can definitely be accessed in whatever Apple calls their service mode though.
And has had a PIN lock from the start. Doesn’t help if you leave it as 1234, though.
How would you set that pin on a SIM card in an iPhone?
On iOS:
Settings > cellular > SIM PIN
Thanks!
True, although this option loses popularity over the years.
And you can use that phone number to find their full name and address.
*her
Whoa that was a wild ride, worth the read. It’s a sad market that exists, great to see Apple’s privacy and security at work (as an Android user even).
I’m not a big fan of iphones or a lot of stuff apple does anymore, but I’m seriously considering moving back to Apple since Google keeps seeming like a worse and worse option (and I’m just not ready to ready to move to some firmware-hacked or otherwise degooglefied Android system). Yesterday’s article about their privacy lead getting fired/quitting and not replaced is just the latest nail.
I’m saying this as a lifetime Linux user and decently tech competent person who knows all about the different android roms: if you’re considering it, switch to ios as soon as you can. Buy the phone outright from apple, no financing or plan.
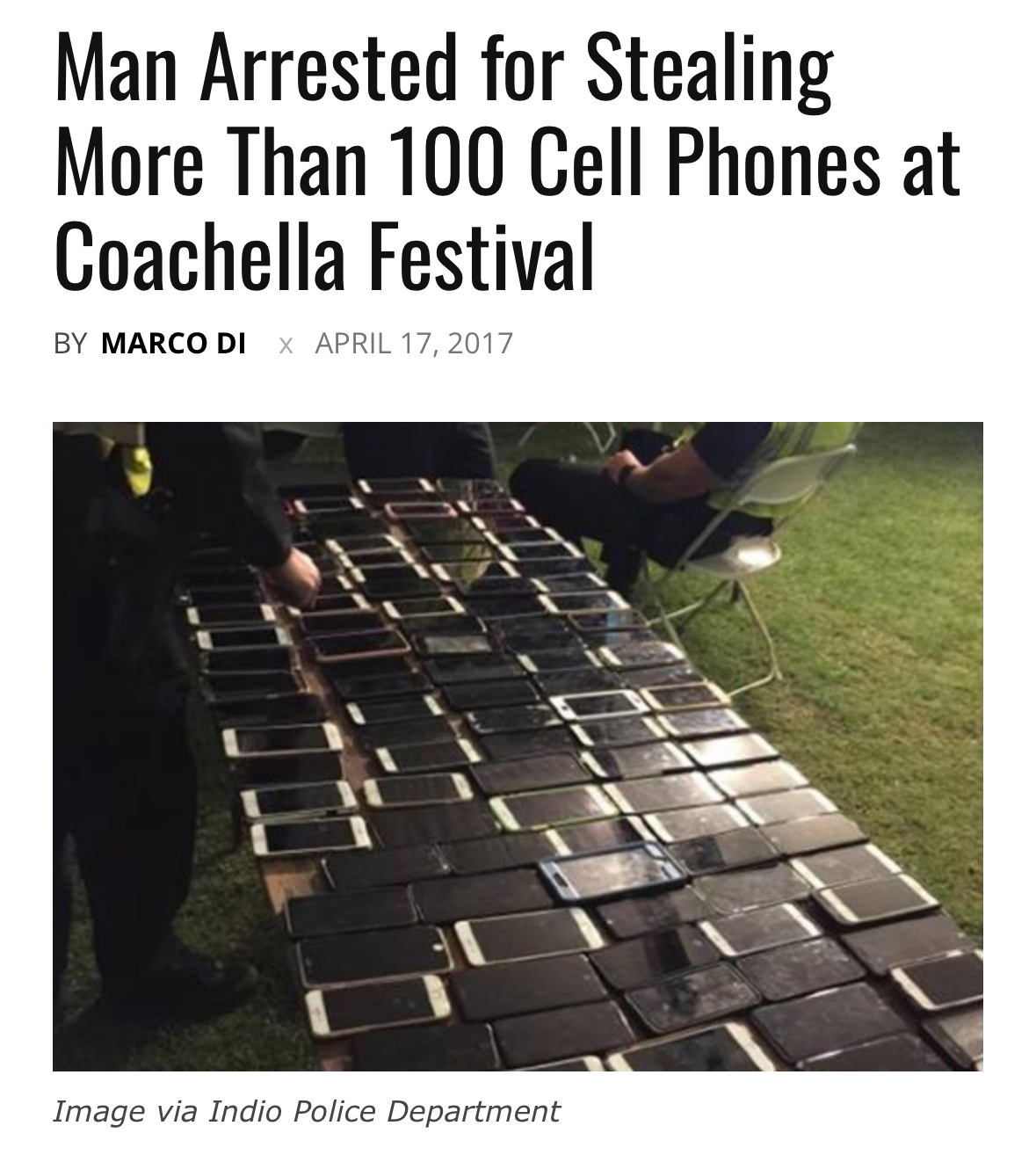
Someone’s going to sell your phone on the black market
is my favorite
Oh no! Then I won’t have my phone anymore!
Wait just a second…
Why doesn’t anything this interesting happen to me!
As the author found out, these phones end up in Shenzhen. You can buy these burnt logic boards on the cheap and lots do just for testing. Check out Strange Parts on YT, he has soldered lots of boards and shows they sell them in bins. The grey market is the only place for them.
Also, for those that aren’t familiar with how Apple’s encryption works. The OS creates a key pair when you create your account, fully encrypting the contents. The contents become garbage if the key pair cannot be matched. This means even if you don’t remotely wipe the contents, the data they try to get from say recovery software or whatever, cannot be read. It’s of course good to wipe it remotely in case they guess your PIN, but if they can’t, then the data is gone forever. From a technical perspective, it’s actually pretty cool.
Android uses similar storage encryption (and you can activate encryption for an SD card if you have sensitive data on it), the encryption key is protected by a TPM or Secure Element chip or by ARM TrustZone or equivalent, it checks that the OS is unmodified before booting and the chip only gives the key to the CPU if the user enters the correct PIN
As someone who’s experienced the same thing, some of the messages I received were shockingly well written.
The fake “find my” site they tried to use to convince me to log into my iCloud account was wildly convincing, if not for the index.php at the end of the URL - something Apple would never configure for service endpoints.
They continued to try - but never threatening. However I never engaged and eventually they just stopped trying.
yeah and the said part is most people without the tech background would never notice the index.php in the URL, or care.
The article does not mention reporting it to the police. I get that 99.99% of the time, nothing will come of it, but that’s something I would immediately do. Maybe I just don’t get the rich aspect of going out and buying the newest latest model right away and forgetting about the stolen phone, even if it is theoretically still in the reach of police forces.
What are the police going to do about your phone?
“Yup. It sure is gone now. Have a nice day.”
“it’s a civil issue”
“It’s a shame about the Credence”
It’s literally a waste of my time to report it to the police. Plus I ain’t speaking to the police unless I’m under arrest and even then it’s to say no comment.
Sure if I see someone get murdered or a something serious then sure I’ll speak, but generally the police can get to fuck. They’re not friends and I’ve only ever had bad interactions with them.
99.99% seems optimistic. You’re gonna have to buy a new phone regardless, if it’s stolen then it’s gone. You can either wait a few days and then buy a new one, or you can just buy it right away
Why would anyone ever interact with the police unless it was absolutely required? They’re not gonna care about your phone, and they might shoot your dog in the process.
ACAB
You should never ever ever purposefully attempt to interact with the police.
Stop resisting!
yeah, let’s invite armed thugs to your location, then piss them off by asking them to help find your precious. unless it’s for insurance purposes, leave police out. if you have 1 problem, and call police, now you have 2.
No joke my dad found a phone while on public trans on his way home from work and 2 hours later the cops showed up knocked and asked for the phone.
Owner choose not to press charges.
I live in a major US city. Who knew!
There’s no point in reporting this to the police in the US. They literally do not care and will not do anything about it.
This made me realize, as an android user, I have no idea what I’m supposed to do if someone steals my phone.
They have the same system. The phone is tied to your account and you can track, lock and erase it remotely with Google’s Find My Device.
Luckily I’ve only had to use “find my device” whenever my phone decides to catch-up with the TV remotes under the couch cushions
We have a black coffee table and sometimes it’s just on the coffee table and I’m like “Jesus fucking Christ what is wrong with you.”. In fairness to me, it’s summer, I keep the shades drawn, keeps the temps down.
Except you can more easily wipe the os at a low level and fully factory reset the device. That’s not possible with iPhones.
Funny thing, even if you do that you can be prevented from initializing the device. You get a “this phone was reset in an unusual way, sign in to the original account used for setup” message the may or not hint at an email address. I’ve got a stack of them on my desk from former employees that I’m trying to get back into. Pain in the ass for business, good for consumers.
Afaik, that changed a while ago. Nowadays, it should still ask for the google account of the most recent owner.
yeah, factory reset protection, it wipes the user data, but will refuse to fully finish setting up the the os after the reset until the google acct is verified…
You can’t do that on modern phones with locked bootloader. This is the reason why manufacturers who allow bootloader unlock still don’t ship phones with bootloader unlocked by default.
hopefully you have it locked so they just wipe the data. and then you buy a new phone.
Google has the same thing
Encrypt it with a strong password in the first place…
Uhg! It’s outta control.
Does anybody have ideas for an anti-pick-pocketing solution they’d like to share? I might have to start a community for it. Or maybe you know some forums where designers who may be interested might be hanging out.
Requirements:
- retrofit almost any front pants/shorts pocket
- allow for near instant access (allowing for e.g. snapping a photo before the moment passes)
- one-handed access
- mechanical/passive: non-battery operated or fails in “unlocked” mode
- if not locked to owner’s hand (or say a finger-worn key), makes removal feel obvious
- automatically resets (resilient & inebriated person approved)
- ideally works with any phone case
- relatively inexpensive, and potentially even open source and/or 3D printable
Lately been imagining something like this, kinda… not really, and with only 2-3 fins:

so you gotta pull your phone out in a way that stretches the pocket to max width and one fin noticeably rubs against your leg.
Doesn’t meet all the requirements but also thought about a long and wide strip of cloth sewn at the bottom of a pocket that you could tuck into your waistband.
Edit: aware of one existing solution but not a huge fan

Honestly you can get a lot done just by wrapping a rubber band or two around your phone, it’ll kinda catch and hold in your pocket and make it more notable if someone tries to pull it out. Works for your wallet too, and all without building a whole ass mousetrap for your pocket.
Oh dude great idea! Also if you did it with hair ties you could keep extra hair ties that way! (Albeit stretched out)
Velcro sewn to just inside the top of your pocket, so sticking a hand in your pocket makes a loud noise and you can feel it, for any pickpocket to separate the velcro.
Mouse trap phone case. It fulfills almost none of the requirements, but it’ll be satisfying when a thief gets snapped.
Decoy phone that is actually a tazer, real phone in underwear.
Don’t get them mixed up…
Yeah it’s great the first time it works but then you have to spend 5 minutes looking for and assembling all the bits and pieces to set it up again.
Also might wanna try to just bring a cheap phone you wouldn’t mind to lose just in case you do manage to lose it. Back up your data so if it does go missing you’ll have the memories.
That’s a great idea! Thank ve thought about carrying a decoy wallet before, but a decoy phone is also a great idea
Not a bad strategy at all.
Still, hate to negotiate with terrorists. And bring home potato photos. Instead of $developing-nation-per-capita-GDP phone quality photos.
Which of course means the thieves will still be tempted! If anti-pickpocketing strategy becomes too successful, they’ll move to violent means, then a cheap phone will be a must.
Well phones are generally pretty good for taking pictures and videos. A pixel 4 or something is a pretty decent phone for example.
Cargo shirts obviously. Those zippers have a purpose!
I use a fanny pack at large events.
Many have hidden zippers for wallet and phone, and its in front of you so its hard to steal from.
Thanks, phone theft is rampant in nightclubs as well and would be great to solve for the pocket problem.
Do like these guys (who I think spend a lot of money on marketing):

I got a cheap one from Amazon.
A key thing a look for are those little nylon pulls on the zipper handles. You can always add them to a zipper as well.
You can loop the pulls through each other to make it harder to open a zipper. I do this for backpacks since they’re behind me. This is more of a deterrent than a lock though.
I’ll send a pic after work to describe it. (Although there are actual products but I am cheap).
Just a phone case with a retractable tether would work fine. Put it in your pocket. Tether is out of the way, completely invisible. Pull it out, tether extends enough to use it, and reteacs when you’re done. With a clip or strap, you can attach it to just about any outfit easily enough.
Realistically, if you have to have a phone somewhere like this where pickpocketing is likely, id suggest either a cheap phone you can lose, or keeping your phone in your hand/a hand on it in your pocket.
I also fucking hate Apple, with the same seething rage that redhats hate Windows, and I too must admit this is shockingly effective security.
Is it though? The author of this article knows what they’re doing, but a regular person would probably not be as relaxed with some of the threats. I didn’t see this in the article, how does the thief have the ability to contact the victim?
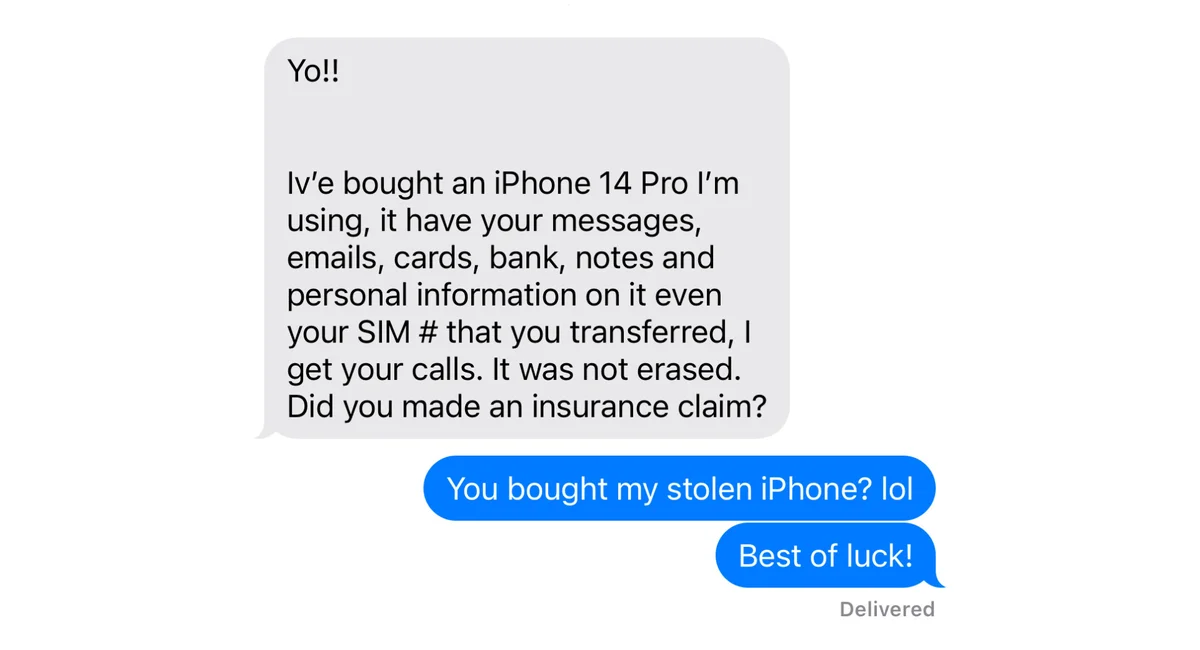
when you end up with someones iphone (or mac or ipad or whatever) and you want to wipe it, the computer needs you to enter the credentials of their icloud account. it tells you whose icloud credentials you need, just like having the username entered but asking for the password.
icloud usernames can be used to send imessages to the owner of the account, like you could call someone with their phone number or IM them with their screen name.
the idea is that a thief ought not be able to just wipe and repurpose a stolen device but a gifted or purchased device should provide a method to contact the person so the new owner can wipe it.
it works pretty good because if a local thief contacts you trying to get you to let them have your device you can call the cops and you already have a line of contact with the person who has the stolen goods so the police can’t even say “yeah whatever, we don’t care, its gone heres some tissues” and it’s very easy to track them down. it also works great if you buy a used device from someone and they won’t clear it to wipe because if you have a transaction record like on ebay or facebook marketplace or something you can also go to the authorities and say “hey, i bought this, here’s proof, and the person i bought it from won’t relinquish ownership of it”
what happens now is thieves ship a bunch of phones off to somewhere outside the juristiction of the victims governments and then they break em down to be sold for parts. now there’s nothing the authorities can do and the thieves accomplices can try to socially engineer the victims into giving them what they want with impunity.
that’s whats happening in the linked article, the victim is being harassed by whoever bought their phone from a thief.
Sure. My point was that exposing someone to scams like social engineering is really really bad and far less desirable than keeping an open line of communication for a purchase
Eh, I think the alternative is worse. If you could wipe stolen phones with impunity they’d be even more of a theft and fraud target than they already are and if they were just locked down with no way out then it’d be more wasteful than it already is.
my experience with iCloud is pretty bad. I worked in a startup at some point which was giving Macs to employees and sort of expected them to figure it out. We had a few people quit and that’s when we figured out that the macs became shiny useless things since we didn’t have access to wipe the associated account and Apple didn’t help in any way. So, from my experience, this is a horrible “feature”.
Now i find out that it’s even worse and it gives 3rd parties means to harass you… I really think that avoiding theft comes at a far to high a price
lol that sucks for the company but that’s what you get when you don’t use some kind of MDM scheme to retain control over assets. It’s especially costly to learn this lesson with Macs though.
I repair and resell scrap computers and if you’re able to prove ownership or have a business that repairs or otherwise handles Mac computers the people at the Apple Store will disable the lock for you. They take down your name and tax id and stuff though, so there’s some accountability, and it’s not easy to get to that point when you look like a greaseball and aren’t a member of apples authorized repair program. Ask me how I know lol.
Tbh it’s no different than a Chromebook or windows laptop that shows the owners email based username (in the case of windows computers with Microsoft ids it shows the users real name as well!) at the login screen, except that you can’t wipe it and resell it.
Oh it could be better for sure. But he’s got access to all the messages and data, getting a number at that point is probably trivial.
As much as I love my android phone, I have to admit Apple takes privacy and security much more seriously.
How so? A Samsung or pixel with default settings would also behave that way, possibly even more securely because it wouldn’t show the thieves your number.
deleted by creator
Removed by mod
Removed by mod
Yes. In the article she states she did exactly this.
If the guy you’re responding to could actually read, he’d be really upset.
deleted by creator
Lol
Dude why even comment?
Removed by mod
I mean, they’re extremely useful and cheap, if you buy the right one.
deleted by creator
They’re not useful? I’m literally using one right now in a way that can’t be done on a dumb phone. Look, I love dumb phones, and I would actually have one if my lifestyle allowed it, but I get so much value out of my smart phone it’s just not practical to use a less capable device.
deleted by creator
You know we can have one without the other if we campaign to make their invasion of our privacy illegal, right?