cross-posted from: https://sh.itjust.works/post/923025
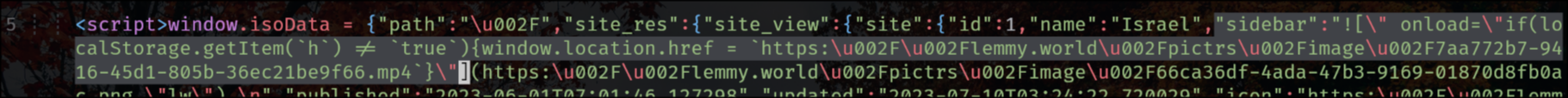
lemmy.world is a victim of an XSS attack right now and the hacker simply injected a JavaScript redirection into the sidebar.
It appears the Lemmy backend does not escape HTML in the main sidebar. Not sure if this is also true for community sidebars.

Wish I knew more about code, I don’t really understand what this means. I did see that blahaj and potentially beehaw have been hacked too, little worried about us
For the moment you can browse with Javascript disabled, though that will disable some functionality of the webpage, or if you have NoScript it stops XSS attacks mostly
Elara said we should be safe, do you think she might be wrong?
Without going into specifics, yes.
well uh oh. Seems like we’re ok for now at least, maybe we should get the admins to shut the instance down
I saw on Hexbear that XSS affected them as well. Do you know how an instance gets targeted by it? The post (on shitjustworks) that I read about it seemed to be related to code execution in the sidebar. So I thought the only way to do this would be if an admin modified the sidebar. But seems like this is not the case from what I read on Hexbear.
deleted by creator
I think it depends, I for one have no idea what other modifications the Lemmygrad team has done to their website, if it’s running stock Lemmy then it’s a chance it might be exploited. From what I’m reading in that thread, the whole Markdown parser doesn’t sanitize things, like this could get interpreted as valid code and run in the user’s browser. The attack on lemmy.world seems just to steal cookies in your browser, thus login credentials, or even more if your browser doesn’t separate cookies. For the moment I would suggest more vigilance when clicking unknown links and such
her claim was that “Lemmygrad doesn’t allow HTML in its markdown parser”
Well yeah we should be fine if there’s not another exploit, I see Hexbear and other instances have already patched it and resetted the login tokens